by Jacob | Jun 24, 2024 | Cyber Security
The cybersecurity landscape is rapidly changing due to zero trust security. It departs from conventional security models centred around the perimeter. This method continuously verifies each connection attempt before allowing access to resources.56% of global...

by Jacob | May 20, 2024 | Cyber Security
Since the development of the internet, many things have changed. The way we bank and access our accounts is one of them. Making deposits and withdrawals from a local bank branch was once required. Checks can now be deposited by taking a picture of them with your...

by Jacob | Apr 29, 2024 | Cyber Security
Keeping up with the latest developments is essential because cyber threats are changing at an alarming rate. It is essential for protecting private data. Threats to data security are growing in sophistication and frequency. To keep up, the landscape needs to shift. We...

by Jacob | Apr 15, 2024 | Cyber Security, IT Consulting, Managed IT
Keeping up with the constantly changing landscape of cyber threats can be difficult. Businesses must handle massive volumes of data. in addition to reacting swiftly and efficiently to situations. It’s difficult to maintain an organization’s security...
by Jacob | Apr 1, 2024 | Cyber Security
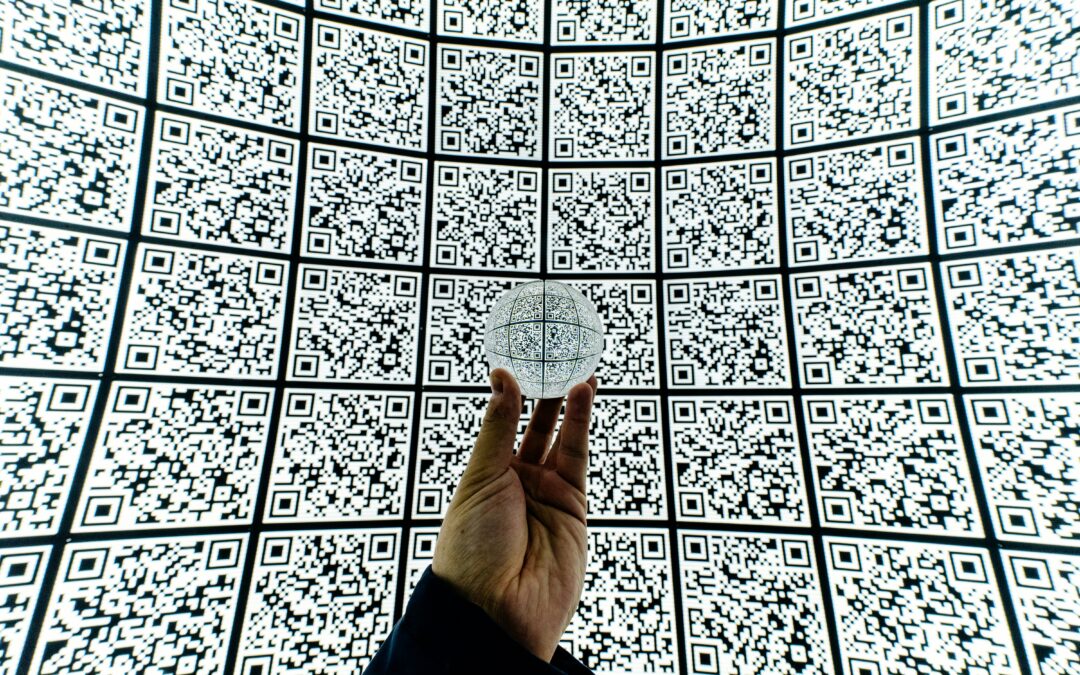
These days, QR codes are widely available. Posters, flyers, and menus from restaurants all feature them. They have online and offline applications. QR codes are user-friendly and convenient. Simply use the camera on your smartphone to scan them. After that, a link, a...

by Jacob | Mar 18, 2024 | Cyber Security, Managed IT
The contemporary workplace is saturated with digital footprints. Workers start producing these as soon as they are employed. They receive application logins and a corporate email address. They might even change their LinkedIn profile to establish a connection with...